
Your Files. Protected.
The All New SpyProof!
Why now? This product was born out of the need to protect intellectual and sensitive private data. Modeled to mitigate the massive losses of trade secrets, future products and Human Resource information about all the employees in a major gaming Studio that occurred from a ransomware attack! This power data breach technology now extends to you in personal worse cases including lost laptops or nosey roomates.
Cyber Security isn't one of those overused buzzwords (looking at you AI) but strategic layers to mitigate loss of much hard work. SpyProof! focuses on protecting sensitive data, meeting regulatory requirements, and safeguarding reputation. More specifically, at the core of the application is secure coding practices, multi-thread protection, memory management and every discipline to produce reliable software and stop bad actors gaining system level access. This propagates to cloud and local data security through the use of encryption to prevent data loss through theft by stolen device, malware, the cloud or Wall Street get rich quick types peeking through stuff they shouldn't (still looking at you AI.)

The Values and High Standards
tl;dr
- Files protected where you need them on your device
- Only one time licensing, no subscriptions!
- Rouge applications are blocked automatically
- Hide private files in virtual storage drives
- Focus on Privacy and Compliance with ISO and NIST Standards not AI
- No SQL, no Active Directory, no Azure AD join required
What was accomplished!
(Updated March 2025)
From the people who have developed and implemented data security for decades against the evolving landscape of cyber security exploits comes the next generational leap enhancing the product portfolio. A product to retro fit end to end data encryption that combines adaptation through transparency, automation and a portfolio eco-system. Only the teams that have kept the title of the premier file encryption solutions status in check would dethrone it for a solution that is the ultra pro max. Welcome to encryption simplified.
This page details everything you need to know about the newest re-invention of protecting your devices data against the biggest threats directly entering your home and work space. Select a topic that most speaks to you to dig deeper.
Hopefully It Is Super Simple to Use Available on both Windows and Linux
Personal, Professional
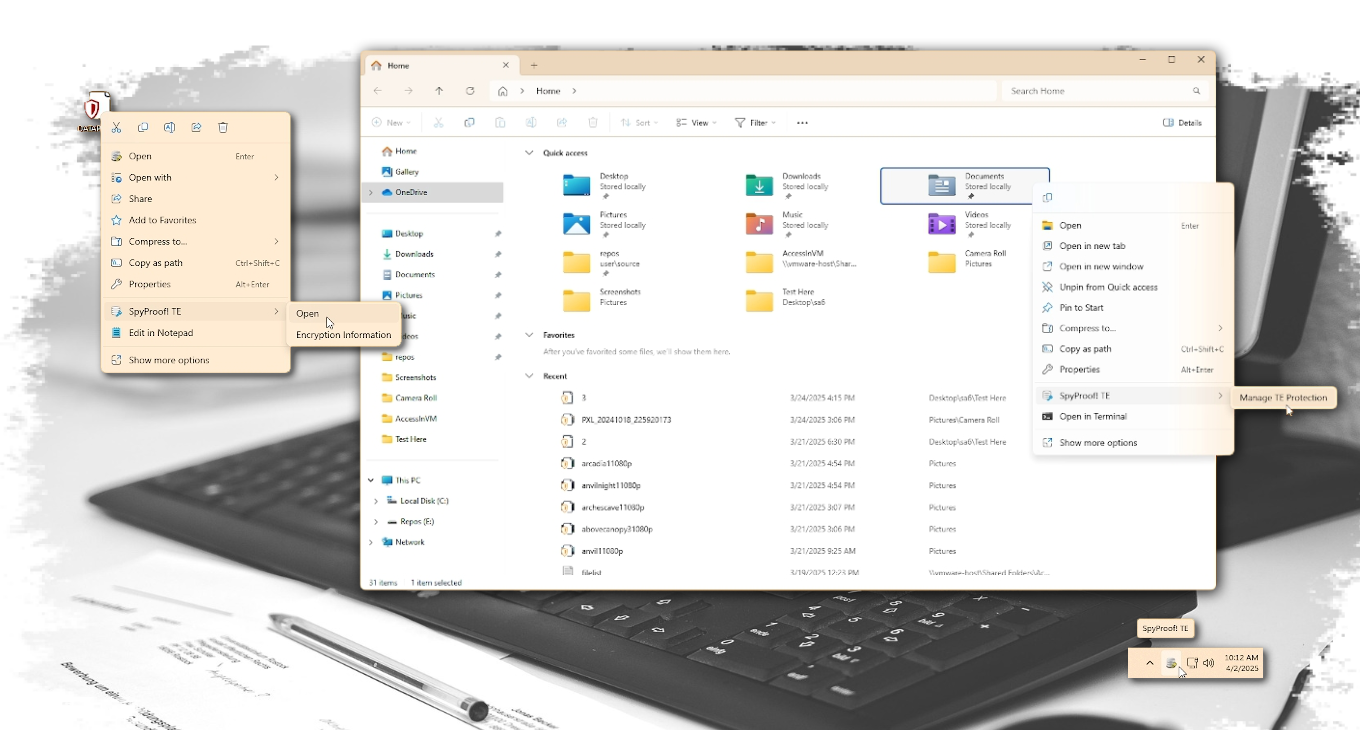
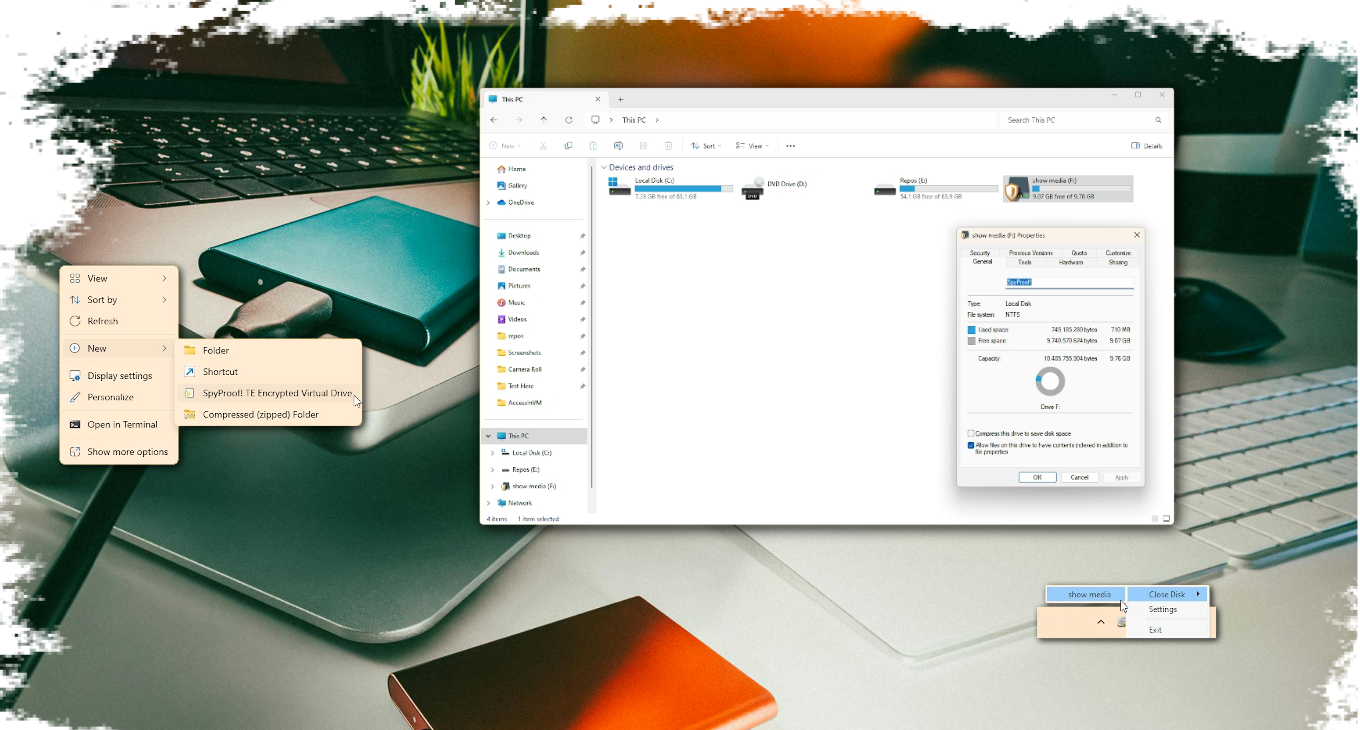
After decades of perfecting the Cybersecurity landscape with the proven encryption technologies of Public Key Infrastructure (PKI), ease of use was our next focus. Dedicated to reaching that target the boldest choice was made: the complete elimination of a clumsy app to deliver our technology. It was a total no brainer that this product is focused on protecting your files so all the functionality should be directly where you focus working on your files. This app now sits quietly with all its other system tray icon friends to only provide you an important notification should one be needed or provide an easy way see an over view of how your data protection is configured. Any other feature you may need only appears where appropriate when you right click on your desktop, file or folder.
How Intrusive is it to Work on My Computer Available on both Windows and Linux
Personal, Professional
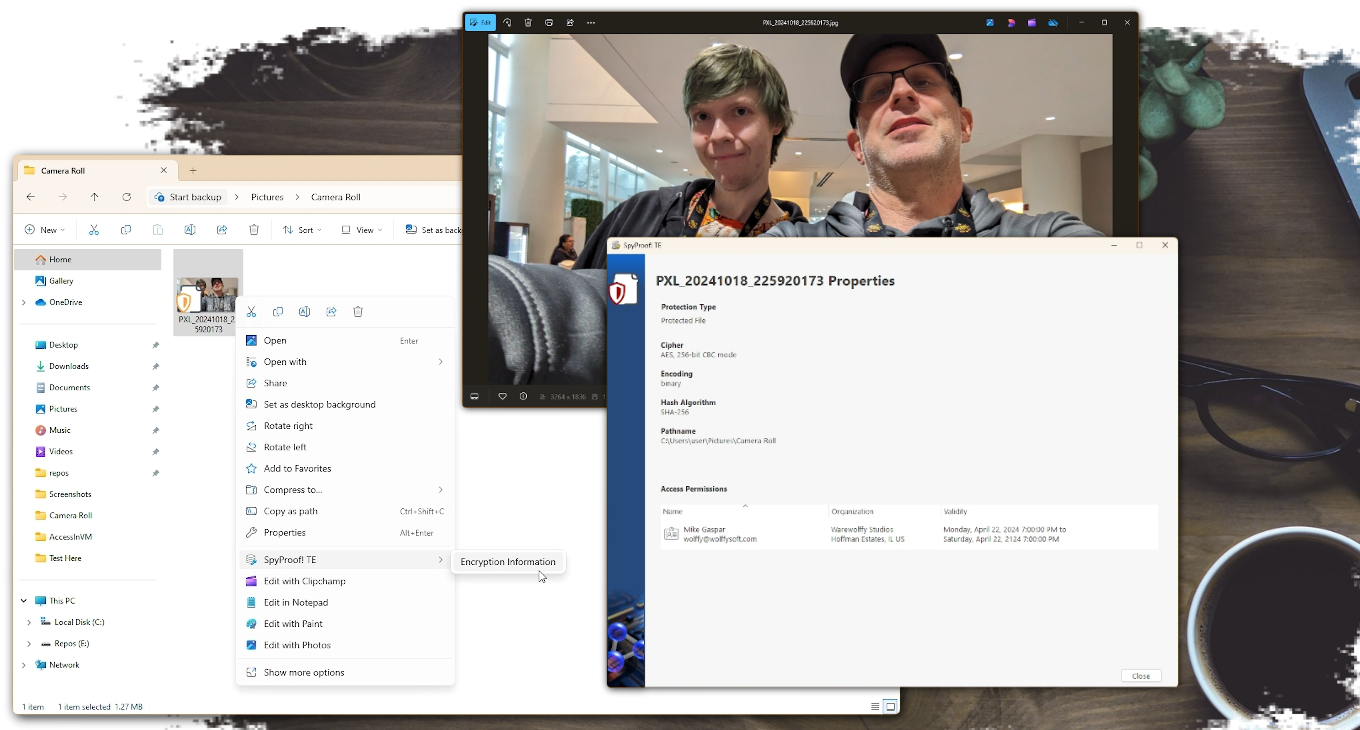
Not at all! A small icon is overlay is placed on the normal icon for your file to indicate that the file is stored encrypted on your storage device. How you use that file doesn't change. Just open the file as you would from File Explorer or from the app itself. Do what you do then save your work.
We know some files are meant to be shared. If you have files that you want to pass around but only protect as it transmit across the vast Internet, we offer a password protection option. Just right click on the file and select this option.
Please note: The password protected option for sharing requires the person receiving the file to also be a SpyProof! customer.
How Does This Whole Data Protection Thing Work Available on both Windows and Linux
Personal, Professional
SpyProof! implements a hybrid cryptosystem. Each file has its own, unique, 256-bit AES (that's means proven strong BTW) key which is protected by the public key from the certificate configured in the profile. When the software is run for the first time it will generate the security professional's recommendation of a ECDH p384 key for you. The resulting certificate and private key are stored locally on your device in the Microsoft Windows key store so it can be protected by your Windows login password, pin or Windows Hello.
I'm Hooked On Using The Cloud, But Those Data Breaches Available on both Windows and Linux
Personal, Professional
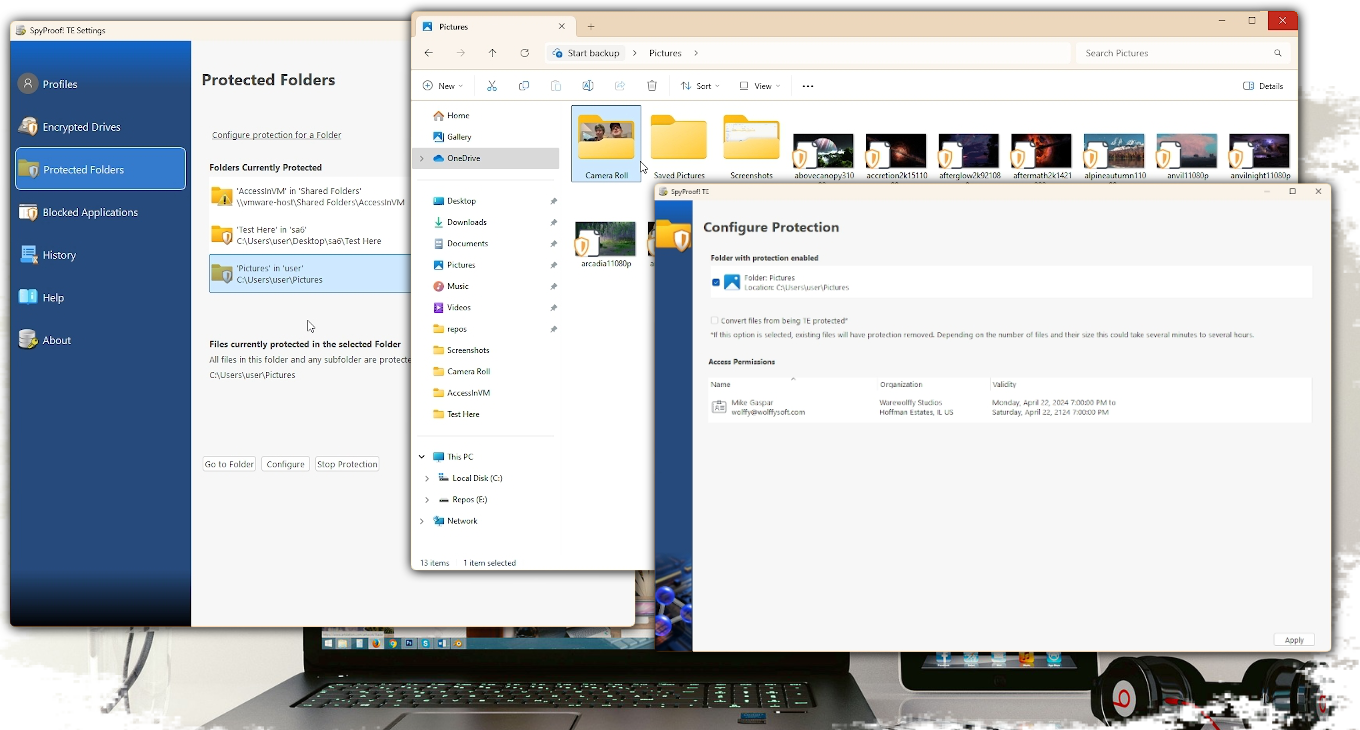
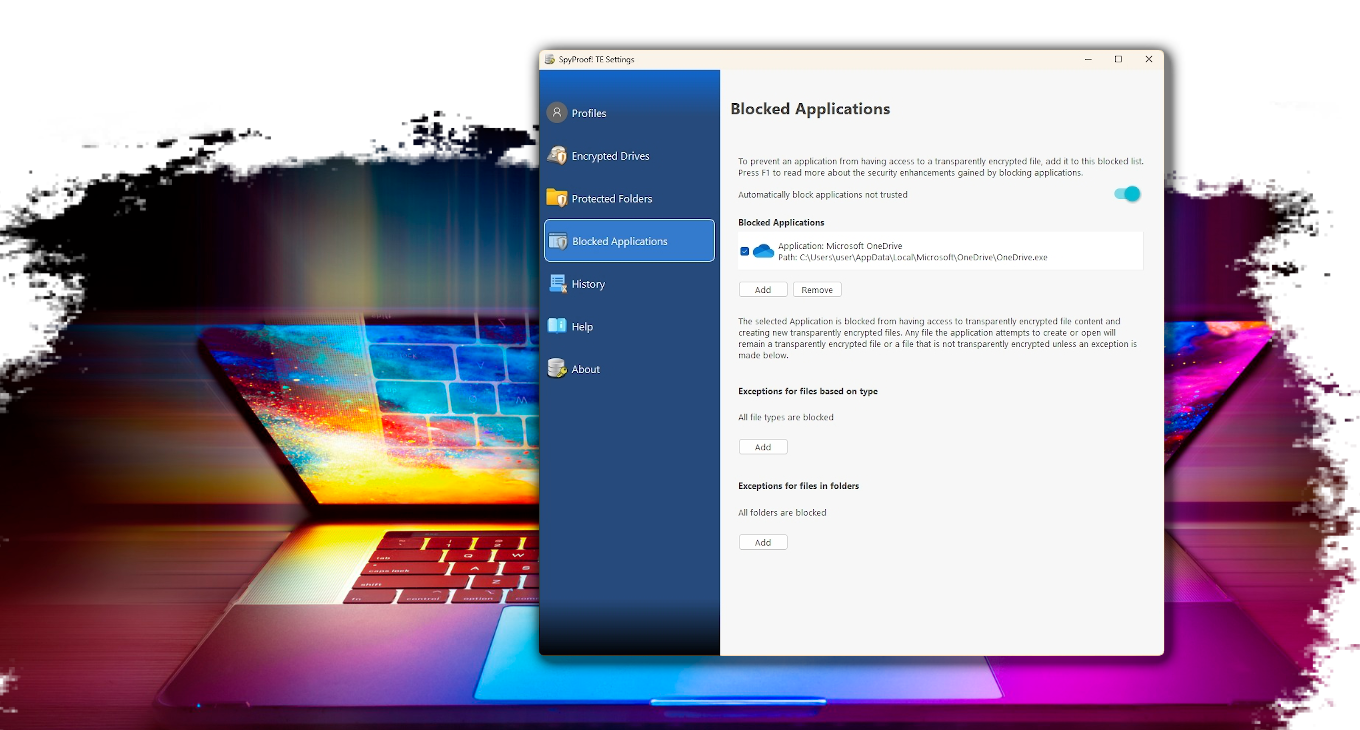
There are three ways applications can be blocked from having access to your files. If at any time you need an application to have access to your files simply unticking the listed app in the Blocked Applications list will stop the block.
- The application doesn't meet Windows requirements as a trusted application. If the application requesting access to your files can not prove it is from a verified provider it will automatically be blocked. This covers most side loaded applications that can be installed, even as SYSTEM, through other software exploits or a harmful e-mail attachment.
- The application is a known cloud back up or file sharing application. SpyProof! has an internal list that is updated through patches to identify these applications and block them automatically to prevent the accidental sending of protected files without the encryption safeguards in place.
- You can add an application yourself! There are plenty of applications out there and you know what works best for you. Just add the application here and it will move, upload or copy your file in the protected state.
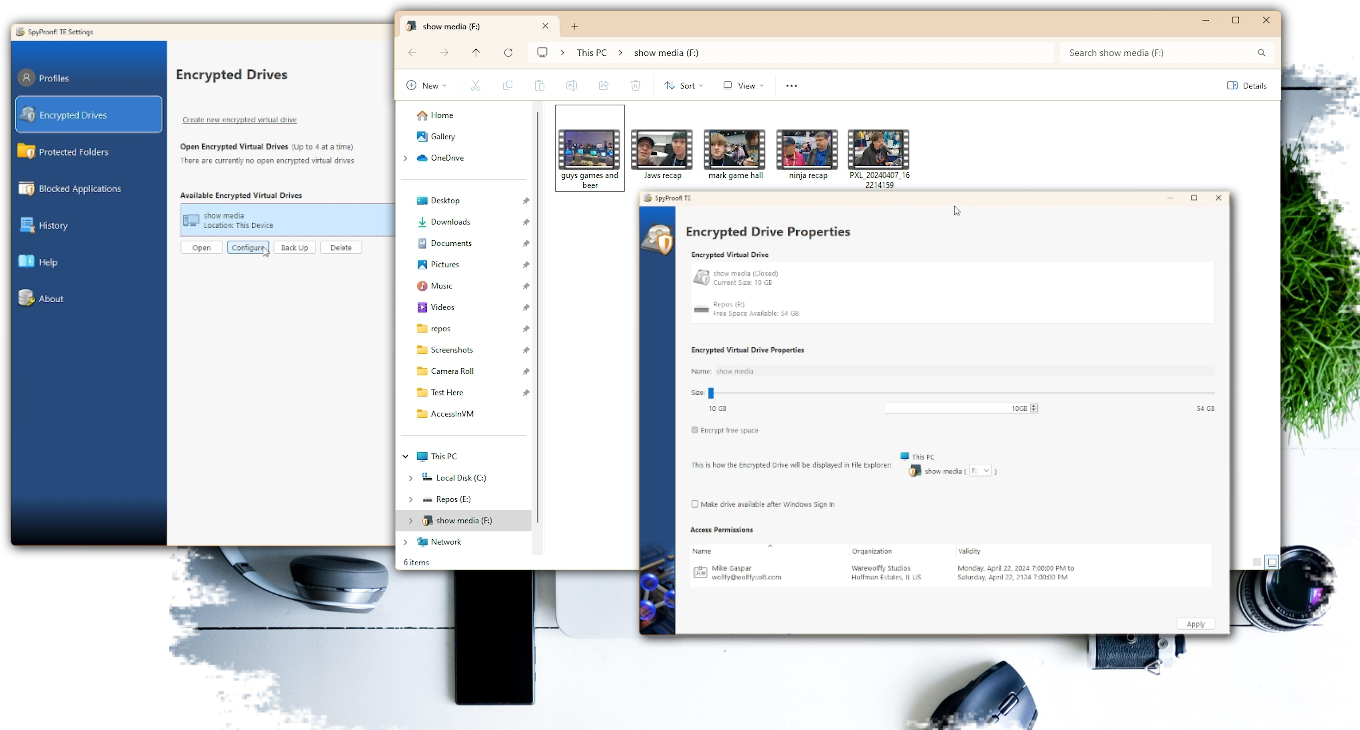
The Folder Thing Is Cool But I'm Thinking More Drive Level Available only on Windows
Professional
Now you are starting to sound like one of our favorite customers! SpyProof! was a product born not just to provide virtual drives, but encrypted virtual drives to bring to Windows the same storage encryption that comes standard in iOS and Android devices. Members of the development team prefer this technology to meet the company's internal data security requirements. Starting with Windows 11 23H2 Microsoft attempted to bring this concept to everyone but still relegated as a more tech savvy feature. SpyProof! makes the creation and use of virtual encrypted drives easier by providing it in our desktop integration and making the drive available when you choose it is needed.
I Have Big Projects That I Back Up Available only on Windows
Professional
The Encrypted Virtual Drives that SpyProof! generates can be as many Gigabytes as you need. The beauty of this solution is that your files accessed on the drive appear in File Explorer, your applications File Open and File Save As windows just as all your other files.
Now plug in a USB Thumb Drive or an external storage device. SpyProof! can create Encrypted Virtual Drives on these storage devices as well. This means you can copy files from Encrypted Virtual Drive to another Encrypted Virtual Drive. But wait, there's more! Plugging the USB Storage device into a computer that either lacks the SpyProof! software or, better yet, has the software but is someone you're not interested in having look through your stuff, there is no visible indication that a Virtual Drive with your important files even exists. This is super handy for those work issued devices where the IT department scans every USB device that is plugged in. Don't entertain those noisy IT geeks with your recent honeymoon photos!
Now plug that USB device back into your own computer and, if you selected the option to do so, your files become available right there in File Explorer. It is like they never left your sight the whole time!
I'm A Nerd Excited by Certification Numbers Available on both Windows and Linux
Personal, Professional
Well... Like the kids today say: You do you bruh!
But there is the list below which should get your motor revving
- FIPS 197: AES Encryption keys 256-bit in size, CBC
- FIPS 186-4 and NSI X9.31: RSA keys up to 16384-bit in size but does size really matter?
- NIST ECDH curves: 256, 384 and 521-bits
- NIST SP800-56A: You know you want this one
- ANSI X9.63: Oh you're getting this one included. No, take it! Gotta free up some storage space
- NIST SP80-90A HMAC: No other HMAC stands a chance
- DBRG SHA-256: That's right 256-bit hashes! YES!
Rather Have A Demo?
Well ask and you shall receive. Let's not leave this product unchartered. Prepare for adventure as we take a tour of your quest to keep your data safe.
It's Your Files! That's It!
With all the news about data breaches, ransomware and scammers out there trying to get access to your digital life isn't it time to put the power to stop data theft in your own hands.